Top 7 React Security Best Practices, Vulnerabilities & Solutions
Last Updated on July 2, 2025
Quick Summary
This guide covers the most common React security vulnerabilities like XSS, insecure data handling, and third-party risks, along with actionable best practices to prevent them. Learn how to build secure React apps with encryption, authentication, input validation, and ongoing audits.
Table of Contents
React is a widely adopted JavaScript library for building user interfaces and powering applications for brands like Netflix, Airbnb, and Uber. According to Built With trends, React holds a 34% share in JavaScript library usage, making it the most popular choice for web and mobile app development.
However, with popularity comes risk. React applications can be vulnerable to threats like cross-site scripting (XSS), SQL injection, broken access control, and insecure dependencies. As an app owner, it’s crucial to understand these vulnerabilities and follow React security best practices.
Don’t worry, our experienced React developers are here to help you build secure, resilient applications.
ReactJS is great for building fast and dynamic user interfaces, but it’s not completely safe from security threats. You still need to be careful of certain vulnerabilities that can affect app security. Below are some of the most common problems in security in React js that you should know.
XML is a data format widely used in mobile and web apps for exchanging or storing data organizationally. To make the information readable and accessible from XML documents, you would require XML parsers. These parsers need a regular upgrade, and being out of update makes them vulnerable to XML External Entity attacks.
XML External Entity Attack is a cybersecurity threat wherein attackers access outdated XML parsers. Cyberattackers perform vulnerable activities, such as port scanning, denial of service, request forgery, and more.
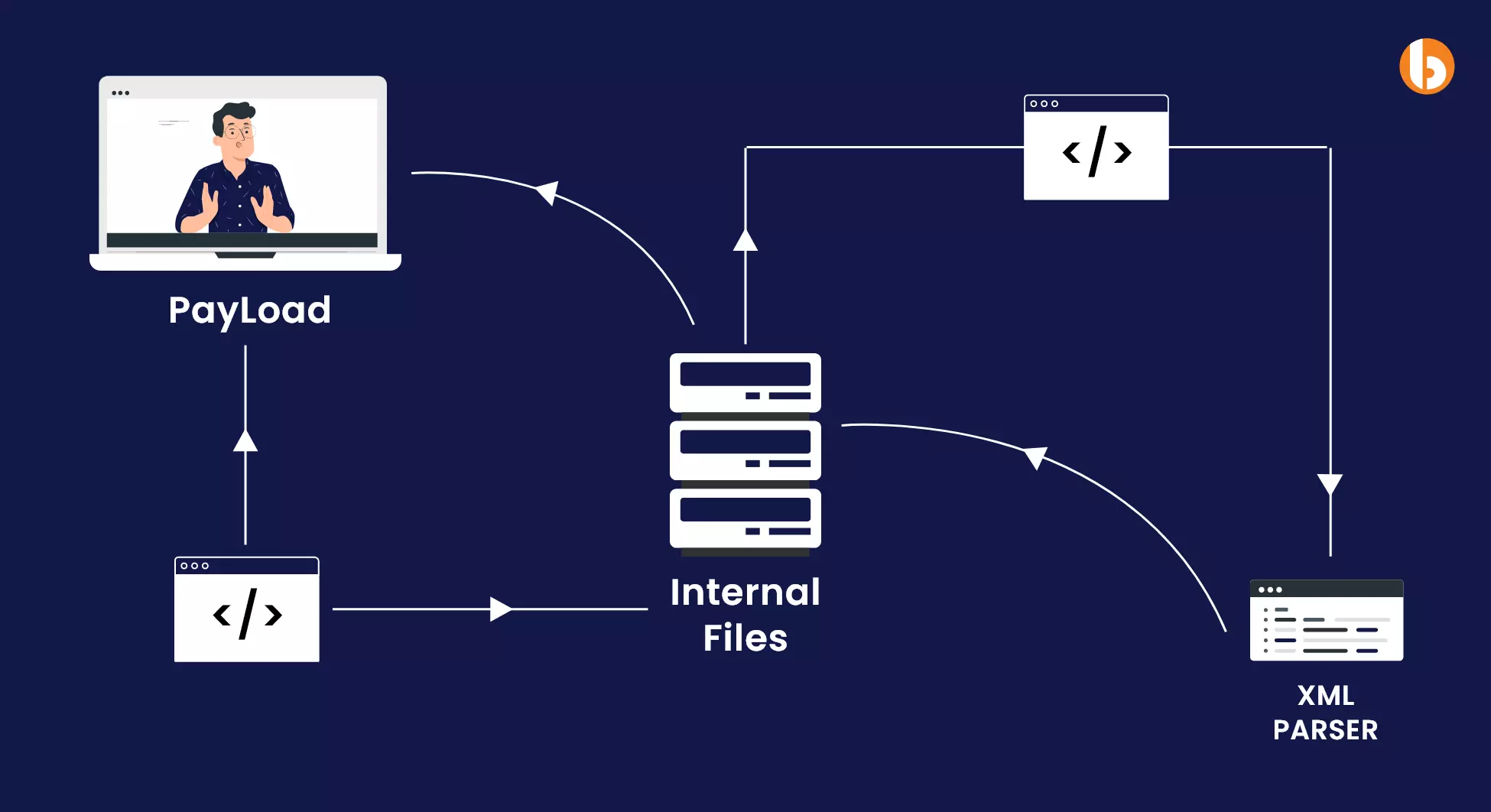
As you know, XML parsers play a crucial role in compromising data; it need to be protected against XXE attacks in the following ways:
The sole purpose of Distributed Denial of Service is to overflood your application, server, or network with massive traffic. The aim behind sending many such requests is to make your application unavailable for target/genuine traffic.
DDoS attacks have different types, such as Hyper Text Transfer Protocol (HTTP), User Datagram Protocol (UDP), Synchronize (SYN), and Internet Control Message Protocol (ICMP). All this is done to exhaust your CPU or server so that it becomes inaccessible for use.
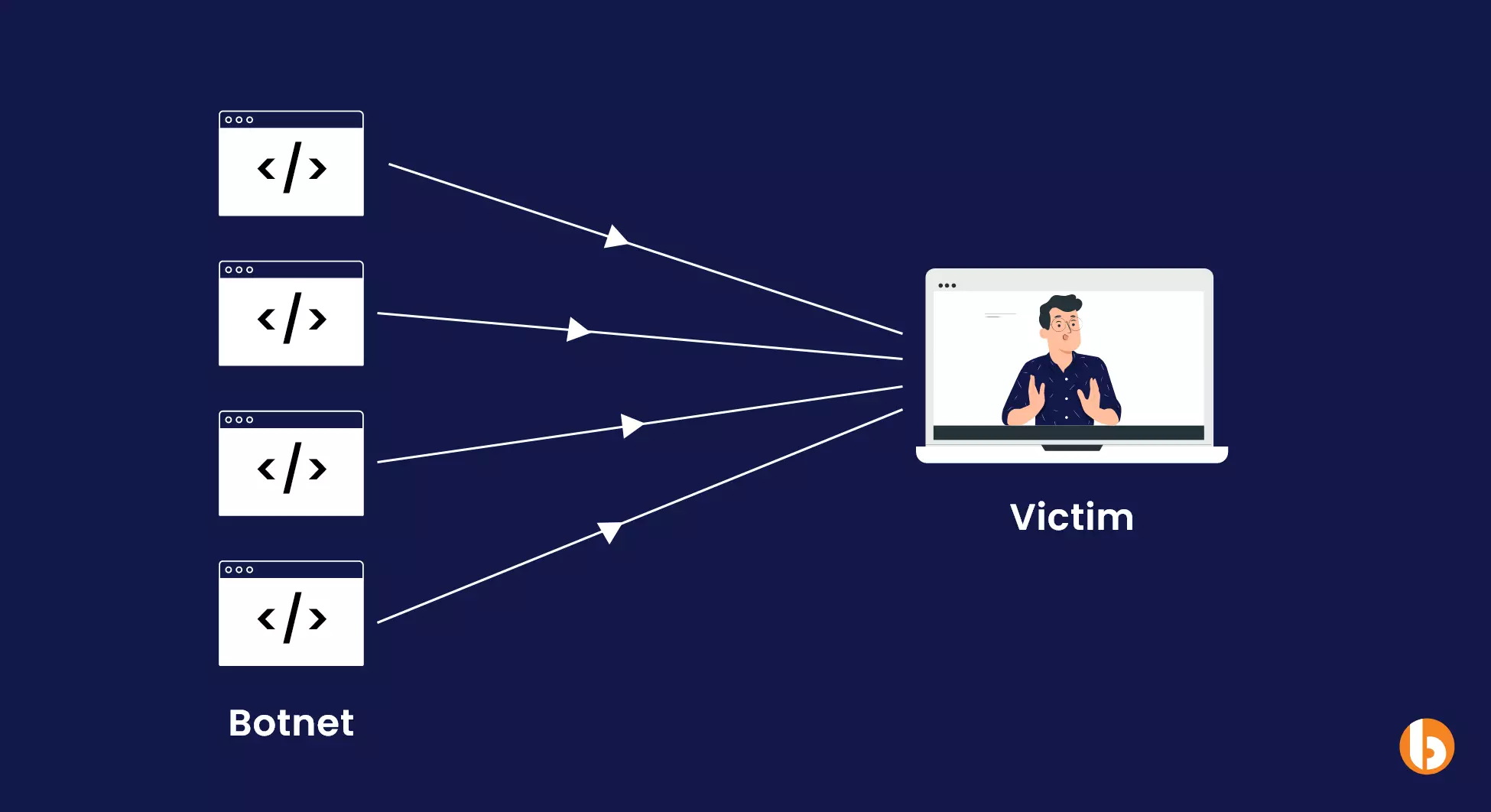
Such security in React attacks wherein your system, network, or website is at risk of excessive, inappropriate traffic requires stringent measures for prevention, which are as follows:
Don’t let a security breach be the downfall of your business
Contact the best React JS Development Company like Bacancy, to keep your React applications safe and secure
Another React js security flaw is the risk of a Zip Slip attack when unpacking files with the help of a supporting library is executed uncontrollably. This is a secret passage through which intruders can execute their malicious code into an unzipped folder(s).
It happens when the user’s browser sends a tampered HTTP request to perform malicious actions. State-changing requests, such as POST, PUT, and DELETE requests, are at high risk since they are more vulnerable than GET requests.

Since CSRF tricks users into performing any action on other websites or web pages, and they gain secret access, some step-wise measures are required to prevent it. Those React js security solutions to the vulnerability are as follows:
When the authentication system of the React.JS application is not designed properly or systematically and does not comply with all security compliance, attackers can easily log into the user’s account.
Attackers usually bypass or manipulate the authentication system and access the victim’s account just like the victim. Broken authentication also occurs when the application allows a weaker password or doesn’t notify about a solid password. It gives attackers easy access to the application or website, enabling them to steal all the credential information.
Since broken authentication is a matter of exploiting loopholes in the authentication mechanism, it needs to be fixed in the following ways:
Tip: implement multifactor authentication for additional security layer
Tip: Do not use obsolete Basic or Digest authentication mechanism
Another React security flaw is the risk of a Zip Slip attack when unpacking files with the help of a supporting library is executed in an uncontrolled manner. This is a secret passage through which intruders can execute their malicious code into an unzipped folder(s). And not only the folder, but the intruder would also even replace folders of other destinations of your React application by taking over the control of your React application.
Through this security vulnerability in React, the intruder would gain access to confidential information of your user base and your business. Zip Slip is an extremely dangerous ReactJS security vulnerability since it exposes your React application to data leaks and path traversal attacks.
These React security best practices are a must-follow while building a React application. If you are planning to develop an application, keep an eye on these best practices. If you are seeking a React developer, you can connect with us.
Let’s discuss 7 ReactJS security best practices.
1. Keep an eye on malicious URLs and URL-based script injection
2. Always sanitize and render HTML
3. Do not directly access DOM
4. Ensure server-side rendering is secured
5. Make sure to use non-vulnerable React versions
6. Make use of the linter configuration
7. Do not use threatful library codes
There can be URLs that might include dynamic script content through the “JavaScript:” protocol URL. Make sure to use “http:” or “https:” against “JavaScript:” URL-based script injection. Besides, you must also leverage a native URL parsing functionality to validate the URL. Post that, make sure to match the parsed protocol property with the allow list.
Here is how to do this:
function validateURL(url) { const parsed = new URL(url) return ['https:', 'http:'].includes(parsed.protocol) } <a href={validateURL(url) ? url : ''}>Click here!</a>
However, do not do this:
<a href={attackerControlled}>Click here!</a>
Use dangerouslySetInnerHTML for HTML insertion directly into rendered DOM nodes. Also, use a sanitization library like domypurify before using dangerouslySetInnerHTML prop.
To perform this, follow the following:
import purify from "dompurify"; <div dangerouslySetInnerHTML={{ __html:purify.sanitize(data) }} />
Never try to inject content into DOM nodes directly. If you are left with only the option of insertion, use dangerouslySetInnerHTML to inject by sanitizing it using domypurify.
Now you must be thinking about what is “dangerouslySetInnerHTML.”
Well, it is a property that helps React programmers to directly insert HTML content within an HTML element available in React application.
You have to do the following:
import purify from "dompurify"; <div dangerouslySetInnerHTML={{__html:purify.sanitize(data) }} />
Tip: Never use refs and findDomNode() to access rendered DOM elements to inject content through innerHTML and similar properties.
Make sure you or your developer never does this:
this.myRef.current.innerHTML = attackerControlledValue;
Use server-side functions like ReactDOMServer.renderToString() and ReactDOMServer.renderToStaticMarkup() for data binding; since it offers automatic content escaping.
When using the renderToStaticMarkup() method in React, it is essential to avoid concatenating strings onto the output before sending them to the client for hydration.
Also, to prevent XSS, ensure you or your developer do not concatenate sanitized data with the output of renderToStaticMarkup().
Do this:
app.get("/", function (req, res) { return res.send( ReactDOMServer.renderToStaticMarkup( React.createElement("h1", null, "Hello World!") ) + otherData ); });
As said in the title, do not use vulnerable React versions. Avoid vulnerable versions of React and React-dom by checking the latest version using npm.
Another on the list of React js security best practices is to install a linter configuration, since it automatically detects potential React js security flaws in your code and advises on rectification.
Make sure to use the ESLint React Security config to identify React vulnerabilities in React code.
Ensure you review library code manually or with the linter configuration to prevent malicious use of security mechanisms.
Make it a point to avoid leveraging React libraries that avoid using dangerouslySetInnerHTML, innerHTML, unvalidated URLs, or other unsafe patterns. Additionally, you can use security linters on your node_modules folders to detect malicious patterns in React code proactively.
Bacancy’s React programmers stay updated with the latest trends, challenges, and solutions. Our developers are on their toes to fix vulnerabilities and check for loopholes that may allow intruders to exploit them.
Following React security best practices and such a solution-oriented mindset would be a great help when you want a website or application that meets customers’ requirements. Rather than making them face glitches and end up with a poor experience.
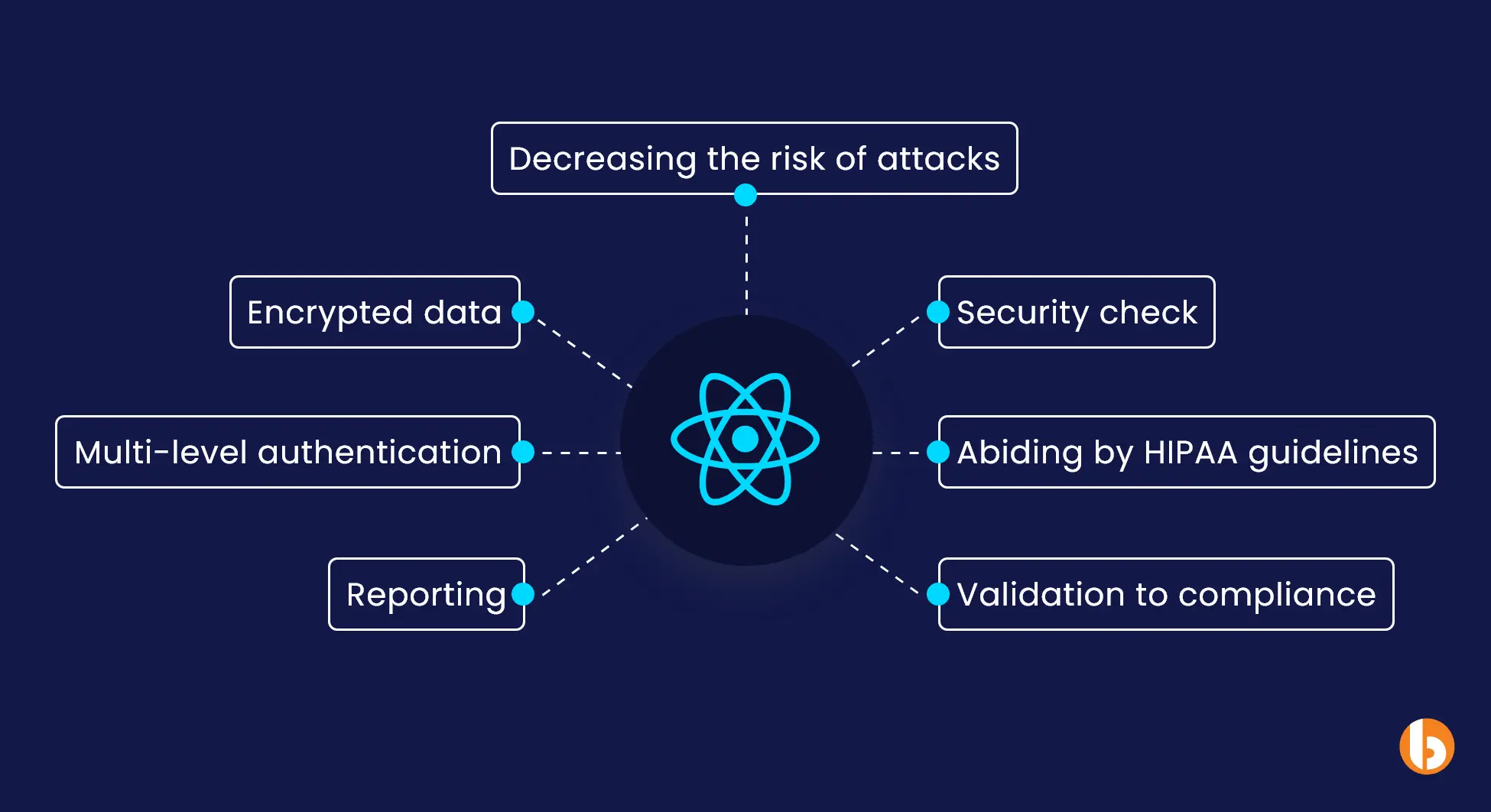
1. End-to-End Encryption
We protect all sensitive data with robust end-to-end encryption. Whether it’s in transit or at rest, our team reduces the risk of breaches, leaks, or unauthorized access. That means your user information stays safe every step of the way.
2. Multi-Level Authentication
Our developers implement 2FA, role-based access control (RBAC), and secure session handling to ensure only authorized users get the right level of access. This layered security approach helps keep intruders out and protects your system.
3. Real-Time Threat Mitigation
We monitor for suspicious activity during development and instantly apply countermeasures like:
This stops threats before they reach your app. By catching threats early, we keep your application stable and secure.
4. HIPAA & Industry Compliance
For healthcare and sensitive data apps, we build to comply with HIPAA, SANS Top 25, and OWASP Top 10, ensuring your app is secure and audit-ready. It helps you meet regulatory standards while maintaining user trust.
5. Behavior Monitoring & Reporting
Post-deployment, we track user behavior and system patterns to detect unusual activity and respond before any damage is done. Our team ensures your app stays secure even after it’s live.
6. Input Validation & Data Checks
Every input is validated for type, format, and values to prevent injection attacks and keep your app logic clean and secure. With strict validation in place, we reduce the chances of code manipulation or data loss.
7. Ongoing Security Audits
Security is continuous. We perform regular code reviews, patch vulnerabilities, and monitor dependencies to keep your app safe as it scales. By staying ahead of emerging risks, our React development team helps you maintain long-term security.
Since ReactJS security vulnerabilities can be difficult to detect, it’s crucial to apply Reactjs security best practices at every layer of your application. Every component needs careful attention to avoid loopholes that could be exploited.
For such critical tasks, you need subject-matter experts. Without their expertise, your application faces a higher risk of security breaches.
You can Hire Reactjs developers from Bacancy and rely on them to address all kinds of ReactJS security issues. Their experience of handling, addressing, and rectifying many React js security vulnerabilities before negatively impacting your brand will come in handy to stabilize and secure your ReactJS environment.
You have to use curly brackets {} to protect against XSS attacks. Keep in mind that the protection layer is limited to rendering textContent and not rendering HTML attributes.
Since React is open-source and lacks strong security settings, it makes the technology vulnerable to different security challenges.
There are several ways to secure react applications from vulnerabilities:
1. Avoid using dangerous URLs
2. Do not serialize confidential data
3. Use direct DOM access
4. Make sure to render HTML
5. Make sure to inject JSON state
6. Make sure to render server-side
Your Success Is Guaranteed !
We accelerate the release of digital product and guaranteed their success
We Use Slack, Jira & GitHub for Accurate Deployment and Effective Communication.