SaaS Security Best Practices and Challenges Decoded
Last Updated on April 2, 2026
Quick Summary
Software-as-a-Service, or SaaS, is revolutionizing how businesses operate in today’s rapidly changing business landscape. SaaS applications and solutions have become integral to modern businesses, regardless of the size and industry, offering unmatchable flexibility, convenience, and scalability. However, most SaaS products provide cloud-based solutions, and with the rapid adoption of SaaS, the need for robust and reliable security mechanisms arises to ensure the security of SaaS applications. To deal with such security concerns, we will delve into the world of SaaS Security and its importance for SaaS product owners and explore the fundamental principles, challenges, and best practices to safeguard sensitive business information against growing cyber threats and attacks.
Table of Contents
SaaS security refers to processes, measures, and technologies leveraged to protect valuable data, applications, and systems from unauthorized access and data breaches. Most businesses and organizations are moving towards using cloud-based infrastructure and environments instead of on-premise systems. Hence, understanding SaaS data security is of utmost importance. Businesses implement a variety of best security practices to safeguard their assets from cyber-attacks using SaaS architecture.
From monitoring a considerable amount of user data to maintaining robust security measures, SaaS business owners must actively look up any security vulnerabilities and threats. As opportunistic cybercriminals are continuously targeting SaaS applications, it is crucial for organizations to prioritize SaaS application security initiatives. All users and customers entrust their personal information to SaaS businesses, which further entrust such critical data to cloud platforms. Thus, SaaS security becomes essential to protect such data against potential security breaches.
Although SaaS solutions will provide marvelous benefits to businesses, including flexibility, cost-effectiveness, scalability, and high availability, it will be beneficial for business owners to focus on security concerns. As enterprises are inclined toward cloud-based Software-as-a-Service solutions, they should prefer a SaaS product with a well-designed architecture. A flexible and scalable SaaS architecture is capable to offer exceptional security and adapt to new threats in real-time. It is incredibly crucial to be aware of the importance of SaaS cyber security. Here are some points to understand why SaaS security is vital for SaaS product owners:
➔ Protecting Data and Information: One of the primary reasons why SaaS security is crucial for SaaS businesses is safeguarding sensitive data and information. Companies work on various confidential information, from customer data to financial statistics to intellectual property. Appropriate security measures will protect such valued information from data theft or damage.
➔ Defend Against Cyber Attacks: As you know, cyber threats and malicious attacks are increasing daily. Businesses are growing under constant alertness to prevent their sensitive data from hackers. Hence, robust SaaS app security mechanisms are essential to defend against cyberattacks by effectively identifying and mitigating potential threats.
➔ Ensure Business Continuity: Data breaches and unauthorized access may lead to data loss, and hamper productivity, revenue, reputation, and customer faith. However, businesses can ensure business continuity and seamless operations by implementing SaaS application security measures to prevent service disruptions, data theft, and server downtime.
➔ Maintain Customer Trust: Customers are aware of the rising cyber crimes and are more concerned about securing their personal information. SaaS product owners are responsible for maintaining customer trust and brand reputation. Even a single data breach can drastically affect business revenue and market share, let aside the loss of customers and clients. But with the efficient security of SaaS applications, you can assure users that their data and information are in safe hands, preventing customer trust from shattering.
➔ Compliance and Regulatory Requirements: Maintaining optimal SaaS security is important as it helps in compliance with security standards and maintaining regulatory requirements. You can avoid legal liabilities or penalties by aligning your business security standards with industry-specific regulations. It also helps win the trust of your customers and partners in your SaaS product.
Before diving deep into exploring SaaS security challenges and best practices, it will be beneficial to comprehend its fundamental principles. Understanding these aspects will help you comprehensively protect the cloud-based SaaS applications and their data. The basic tenets of SaaS security principles that every SaaS company should adhere to are mentioned as follows:
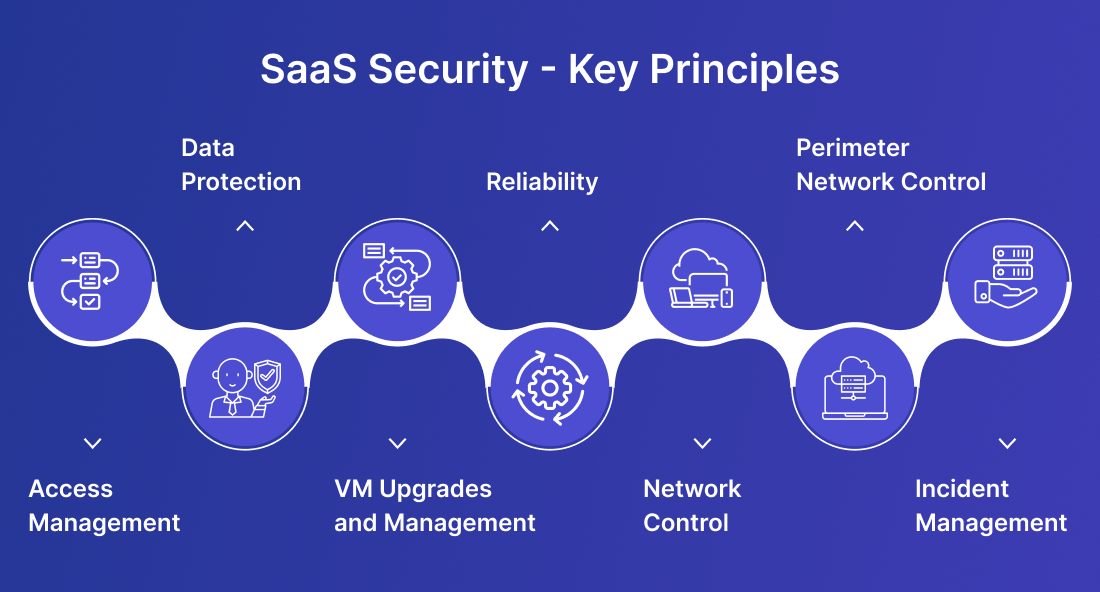
Businesses often deal with sensitive data and information, making it essential to consider access management as one of the most critical aspects of SaaS application security. It will be crucial for security personnel to have robust access management systems with efficient role-based access control, workflow management, and limited administrative access. Hence, only authorized users can access the application data, reducing the risk of data breaches.
Data protection should be the top priority for securing SaaS applications. Businesses should schedule regular security audits to identify and resolve vulnerabilities and implement robust data backup and secure storage solutions to safeguard valuable assets. By adopting these SaaS security principles, businesses can enhance their overall security posture and better protect their valuable data.
Regularly upgrading and updating virtual machines(VM) is crucial when creating a secure SaaS security architecture and infrastructure for your users and customers. VMs would not address vulnerabilities and prevent business data exploitation without continuous upgrades. By maintaining up-to-date VMs, you reinforce your security posture, enhance protection for your users and customers, and ensure the integrity of your data
Users prefer a SaaS security platform that loads quickly, making a high-level Content Delivery Network (CDN) essential. CDNs reduce latency and improve load times by distributing content across global servers. They also enhance reliability with decreased downtime and effective disaster recovery by quickly rerouting traffic during outages. Using a CDN, SaaS businesses can ensure a smooth, responsive experience and maintain continuous access to critical services.
A solid network control strategy is essential for SaaS product owners to ensure robust network security. Reviewing Network Access Control Lists (NACL) helps monitor user access, while a Virtual Private Network (VPN) controls inbound and outbound traffic, mitigating threats and unauthorized access. Andrew Gitt from VPNBrains highlights its importance: “In SaaS, a VPN is crucial for network control, encrypting, and monitoring data transfers to reduce cyber intrusion risks.
Perimeter network control, as the name suggests, controls the security of the external boundaries of SaaS application infrastructure. Businesses should prioritize implementing robust firewalls and intrusion prevention systems (IPS) to prevent malicious traffic and users from entering data centers.
Incident management is a critical component when CISOs need to get instant alerts and responses for specific incidents. An excellent incident management system continuously monitors and tracks malicious activities or incidents, allowing organizations to respond to threats promptly and reduce system downtime.
Well, most modern organizations are adapting cloud-based solutions like SaaS to take advantage of saving the cost of building an on-premise infrastructure. SaaS solutions allow businesses to experience flexible, customizable, and feature-rich applications to improve overall productivity and performance. However, there are several challenges and risks SaaS product owners may face when securing SaaS applications. These SaaS security challenges include the following:
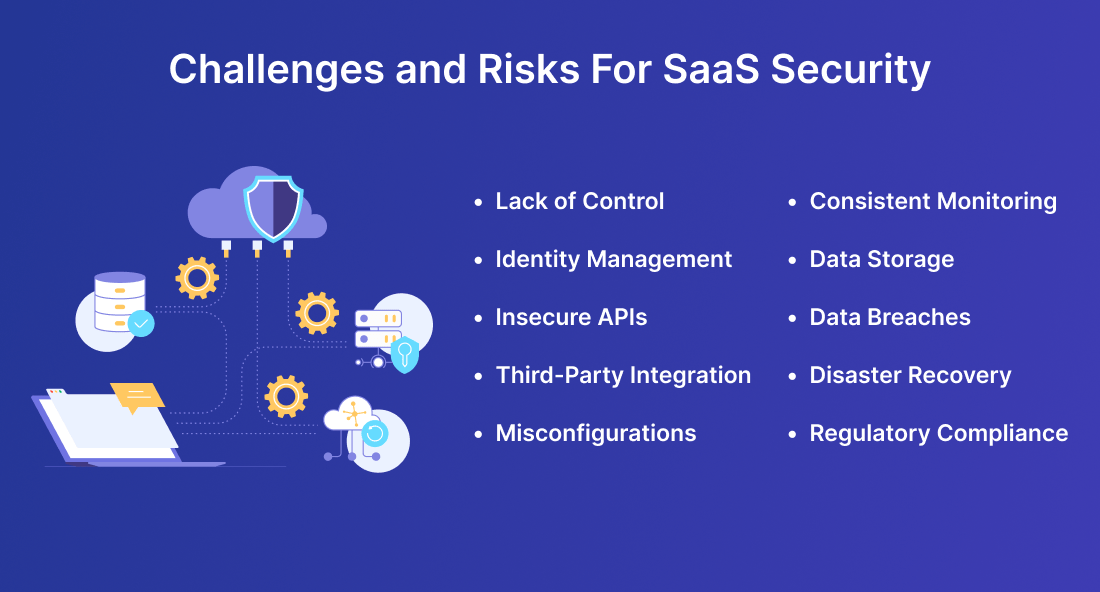
SaaS solutions provider typically hosts their data and applications on cloud platforms. It means SaaS application users or customers would not have direct data storage and management access. Hence, you must rely on SaaS providers if any problem or data management issues arise.
SaaS application users must validate their authentication by logging into the application through their personalized credentials. After successful authentication, the user can access the application data and features. However, user and identity management can be challenging, primarily if the SaaS solution provider hosts applications for multiple users with varied data access demands.
When ensuring SaaS application security, SaaS product owners may have to actively look out for insecure APIs (Application Programming Interfaces). An insecure API can open the back door for hackers to enter and disrupt the secure system. SaaS businesses must safeguard their communication endpoints by implementing SaaS security API tools for vulnerability management and limited API access. For instance, implementing an API scanner to keep tabs on any potentially malicious misuse of third party integrations is a good move, in part because it automates protection of your platform. This prevents insecure APIs from allowing cybercriminals to carry out malicious attacks and unauthorized data access.
Software-as-a-Service solutions often integrate applications with third-party services and vendors for payment processing, data analytics, or marketing platforms. But relying on these external entities introduces additional security risks and incidents as the security vulnerabilities of third-party vendors will affect the existing system. It leads to data exposure and service disruptions.
Secure Your Data, Secure Your Future!
Hire SaaS Developer to develop data-driven, innovative, and secure SaaS solutions that safeguard your business assets and sensitive data.
Utilizing multiple interactive features and functionalities of SaaS applications seems intriguing. However, it will make the SaaS application more complex, increasing the chances of misconfigurations. Even a single coding error can lead to unintentional data leaks and exposure. Misconfigurations make it essential for SaaS business owners to appropriately check the cloud configuration at a regular interval of time.
Another SaaS data security challenge CISOs (Chief Information Security Officers) need to be aware of, is consistent and continuous monitoring to identify and address security threats in real time. Constant monitoring and analyzing system logs, network traffic, data streams, and user activities can be challenging as the data is distributed over different cloud servers. Businesses must allocate dedicated resources with sufficient expertise to take immediate and effective action against potential attacks.
Data storage is also a considerable challenge for maintaining optimal SaaS application security. Businesses must assess the encryption and access controls when storing large volumes of sensitive data and information on cloud servers and storage systems. Also, you can check if the data is stored with the help of secure cloud service providers like AWS, Microsoft’s OneDrive, and any other private cloud service providers. If your business data is stored at multiple locations and shared with numerous organizations, it is crucial to ensure data security and integrity.
Many organizations face data breaches, one of the most common security threats, daily. Accessing, monitoring, or managing sensitive business data without appropriate authorization is considered a security violation or data breach. These incidents can lead organizations to lose data, reputation, and system disruptions. Having robust security mechanisms is essential for SaaS product owners to minimize the risk of data breaches and secure precious data.
Disasters are unpredictable and can happen anytime, regardless of ensuring all security measures and precautions are up-to-date and working fine. Hence, SaaS businesses should clearly know what happens to their data stored on the cloud servers in case of disasters. Implementing an efficient disaster recovery plan will help recover all your important data files and user information if natural disasters or accidental system failures occur.
While managing and maintaining the security of your SaaS applications, evaluating regulatory compliance and governance policies is crucial. It is essential for any SaaS business that its services or products comply with regulatory compliance such as GDPR, HIPAA, SOX, etc. You can also check whether your SaaS solution providers hold security certifications like ISO, ITL, and other credentials.
Remember, every SaaS product deals with a large volume of sensitive user privacy and corporate data. Additionally, this data can be accessed on any device from any location, making it vulnerable to different types of cyber attacks. Therefore, making your SaaS Product secure and compliant is the prime duty of every SaaS owner. Besides, it helps you strengthen the core SaaS metrics necessary to track your business growth.
Now that you know, no SaaS application or system is considered entirely safe unless adhering to appropriate SaaS security best practices and measures. From prioritizing data privacy to identity access management, we will enlist the below tips to ensure and enhance SaaS application security. Let’s review the below best practices utilizing which SaaS businesses can fortify their infrastructure and data servers against potential threats.
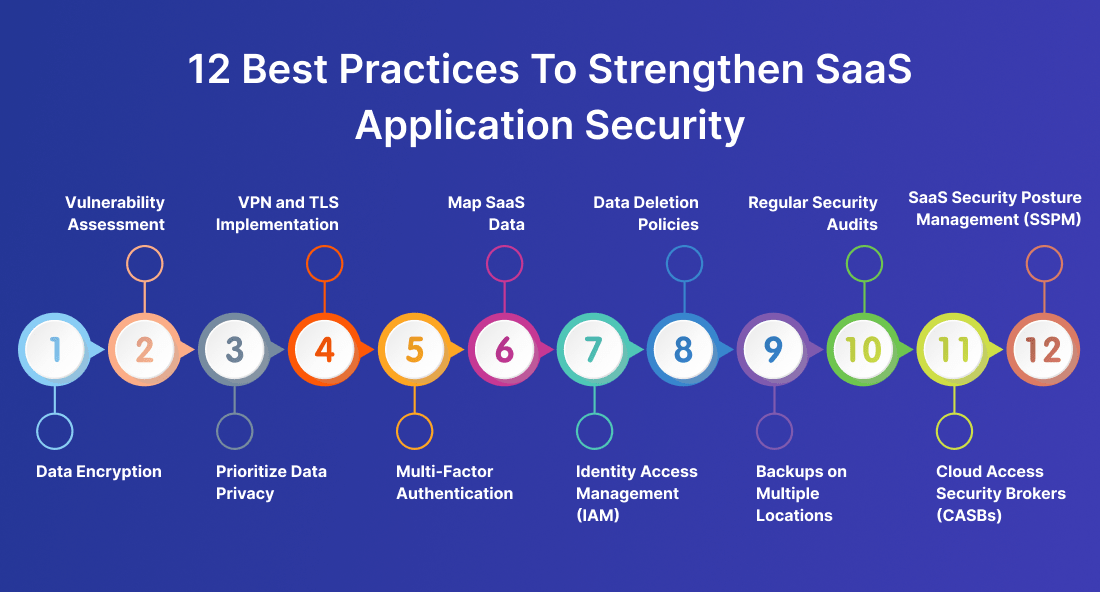
End-to-end data encryption is one of the most crucial SaaS security best practices you should implement to ensure safe interactions. Yes, all the data exchange and interactions between the user and cloud servers must happen using SSL connections and implementing HTTPS protocol. Moreover, you can facilitate various end-to-end data encryption techniques for data storage and management. Also, you should specify the cloud service provider if only specific financial data files or business statistics information is required to encrypt using multi-domain SSL certificates.
As SaaS apps use cloud platforms and servers for data storage, explicitly identifying security vulnerabilities is difficult. Timely vulnerability assessment can be feasible with SaaS application security testing tools. With powerful SaaS security tools and systems, you can safeguard essential data to identify vulnerabilities, including Cross-Site Request Forgery (CSRF), SQL injection, Cross-Site Scripting (XSS), and other cyber attacks.
SaaS businesses must prioritize data privacy by strictly adhering to privacy regulations. You can instruct customers and employees about dealing with valuable data by implementing strong privacy and security statements for your SaaS products and services. Limiting the collection of data and providing explicit consent to users also adds to facilitating data privacy.
VPN (Virtual Private Network) is the perfect solution for businesses that seek safer work environments for clients and employees, leading to securely storing and managing data. Most organizations prefer VPN rather than selecting a straightforward multi-tenant system. By implementing a VPN, you can secure all accessible endpoints to protect your SaaS infrastructure. Additionally, you can use TLS (Transport Layer Security) to improve data privacy while the user interacts with the application. You can also secure internal data by storing it in an encrypted form and passing it through TLS.
Users should have different access control over the data based on their roles. It will make it difficult for cybercriminals to access sensitive business data and information. Implementing efficient multi-factor authentication mechanisms makes it essential for any user to validate the authentication more than twice to access the app data.
Elevate Your SaaS Application Security Today!
Partner with an experienced SaaS development company to protect your product from cyber threats by leveraging our professional SaaS development services.
Data mapping, classification, and monitoring are essential to ensure high-level software-as-a-Service security of the applications. SaaS professionals must analyze it even though the data is in transit, use, or at rest to secure its preservation. It is crucial to understand the data flow within the SaaS system, like how and where the data is stored, processed, and transmitted. To apply essential security measures, ensure the data mapping practices are capable enough to help n identify data exposure and leak points.
With identity Access Management (IAM) solutions, businesses can ensure that the users can only access the information and resources they need. Identity Access Management encompasses authentication, authorization, and auditing to manage user privileges effectively. By setting up user access control as per their requirements and creating robust user authentication protocols, you can ensure users’ authenticity before they actually access the application and data, further reducing the unauthorized access risks.
Data deletion policies are vital in keeping user data and business information secure. Programmatically deleting customers’ data and information is quite a crucial and legal necessity for SaaS businesses. However, SaaS solutions providers must educate customers about their data deletion policies and timelines to maintain customers’ trust when initiating a contract.
As a SaaS business owner, you should know how important it is to manage and maintain customer data effectively. Therefore, backing up important user data and information in multiple locations is viable. Having your data backup in several sites or servers can help you instantly recover or retrieve the data in case of data breaches or system failures. Although many cloud service providers offer backup solutions, businesses must adhere to timely backups to avoid customer data loss.
Regular security audits and assessments can aid in evaluating the effectiveness of security measures and controls. It also helps identify security vulnerabilities, gaps, and areas of improvement. Consistent monitoring of SaaS cyber security incidents may help prevent cyberattacks by utilizing automatic data logging mechanisms and assisting in efficient security audits. Apart from timely security audits and ensuring access controls, you can watch for security threats and issues reported by OWASP.
Cloud Access Security Broker, or CASB, is one of the popular best practices for enhancing SaaS application security. Not only does CASB assist in pointing out members using unauthorized SaaS systems, but it also helps obtain significant data usage and user behavior visibility. Business owners can consider it an additional security and access control layer for SaaS applications. Cloud Access Security Brokers can assist in enforcing data security policies, compliance reporting, security configuration audits, and more.
Security posture means the cybersecurity strength and effectiveness of a SaaS business. SaaS Security Posture Management encompasses numerous tools and techniques to automate SaaS application monitoring to identify security misconfigurations, prevent configuration drift, enhance compliance management capabilities, and overcome other security challenges. It also provides uniform transparency throughout the entire cloud environment. Additionally, SSPM also mitigates the risk of unexpected security vulnerabilities that happens in SDLC (Software Development Lifecycle).
For SaaS business owners, ensuring powerful security mechanisms and measures should be a top priority to safeguard their user data, prevent data breaches, and maintain the company’s reputation. We have curated a quick SaaS security checklist that helps identify and mitigate security risks in your SaaS applications. Follow the below checklist and ensure optimal SaaS application security:
✅ Have you implemented robust end-to-end encryption to protect sensitive data in transit and at rest from unauthorized access?
✅ Did you enforce Multi-Factor Authentication mechanisms to add an extra layer of security and verify user authentication?
✅ Is your SaaS business leveraging the power of Cloud Access Security Brokers (CASBs) to enhance security and visibility in cloud environments?
✅ Do you store backup data in multiple locations to facilitate data availability and integrity?
✅ Have you done proper data access management to limit user permissions and privileges according to their roles and profiles?
✅ Are you conducting regular vulnerability assessments and testing to recognize and address SaaS cloud security vulnerabilities and weaknesses?
✅ Do you ensure to update and upgrade the SaaS software as per the latest trends and technologies?
✅ Are your SaaS professionals conducting regular security audits to evaluate the effectiveness and efficiency of security measures and identify improvement opportunities?
✅ Did you utilize SaaS Security Posture Management (SSPM) tools to continuously maintain, manage, and monitor a proactive security posture?
✅ Have you educated the employees and customers on your company’s security and data deletion policies to maintain trust and faith in the organization?
As the SaaS landscape continues to expand drastically, organizations must better understand the importance of Software-as-a-Service security and take initiatives to build a robust security environment for their employees and customers. We hope this provides you with greater clarity on SaaS security best practices, principles, and challenges.
By comprehending the potential difficulties of SaaS app security, you can proactively deal with security threats, mitigate risks, and safeguard sensitive data. Additionally, businesses can ensure unparalleled SaaS application security by adhering to best practices, such as vulnerability assessments, identity access management, utilizing data backup solutions, and regular security audits.
Leverage our expert SaaS consulting services to avail the benefits of cloud-based solutions. We offer you guidance that lets you stay ahead of the curve and ensures your data and infrastructure are securely protected from potential threats.
SaaS security protects user data and privacy by following several security best practices, techniques, and technologies. It is crucial to have strong SaaS cloud security for businesses if you intend to secure corporate data in cloud-based applications. It will help counter the risk of security breaches, unauthorized access, and potential threats.
To enhance SaaS application security and fortify your SaaS business infrastructure, consider implementing data encryption techniques, multifacet authentication, user access controls, and regular security audits. Ensure your SaaS business has essential security certifications and complies with industry regulations.
The key SaaS security best practices include Identity Access Management (IAM), prioritizing data privacy and security in SDLC, and ensuring reliable data recovery backup solutions. Other SaaS security practices like implementing VPN and TLS, compliance with regulatory standards like HIPPA and GDPR, and end-to-end data encryption can be beneficial to strengthen the security of your SaaS business.
Your Success Is Guaranteed !
We accelerate the release of digital product and guaranteed their success
We Use Slack, Jira & GitHub for Accurate Deployment and Effective Communication.