Mastering Hybrid Cloud Security in 2026: Components, Challenges & Best Practices
Last Updated on February 6, 2026
Summary
This blog uncovers the fundamentals of hybrid cloud security, provides a clear view of its architecture, and highlights the key components necessary for effective protection. It also addresses common security challenges and shares actionable best practices to help organizations build a resilient and future-ready security posture for 2025 and beyond.
Table of Contents
A hybrid cloud is a mix of public cloud, private cloud, and sometimes on-premise systems. It allows sensitive data to stay in secure environments while using the public cloud to scale quickly and handle dynamic workloads.
However, this blend of environments can create numerous security challenges. With data and applications spread across different platforms, managing access, monitoring activity, and ensuring consistent protection becomes increasingly complex.
To keep hybrid environments secure, organizations need a connected approach that secures data, applications, and identities across public, private, and on-premise platforms. This requires clear policies, strong identity management, and real-time threat detection that work across all environments.
In 2025, hybrid cloud security is more important than ever. In this blog, we will look at the key aspects of securing a hybrid cloud and how you can protect your systems effectively.
Hybrid cloud security refers to the tools and processes used to protect data, applications, and systems in a hybrid cloud environment. This environment may include a mix of public clouds, private clouds, and on-premises data centers.
A strong hybrid cloud security setup typically includes the following:
The hybrid cloud security architecture combines multiple types of firewalls, physical, virtual, and containerized, to protect workloads across both private and public cloud environments. These firewalls are strategically deployed to ensure end-to-end protection of data, applications, and systems.
This diagram represents a Hybrid cloud security architecture, showing how firewalls (both physical and virtual) are deployed across private and public cloud environments to protect workloads.
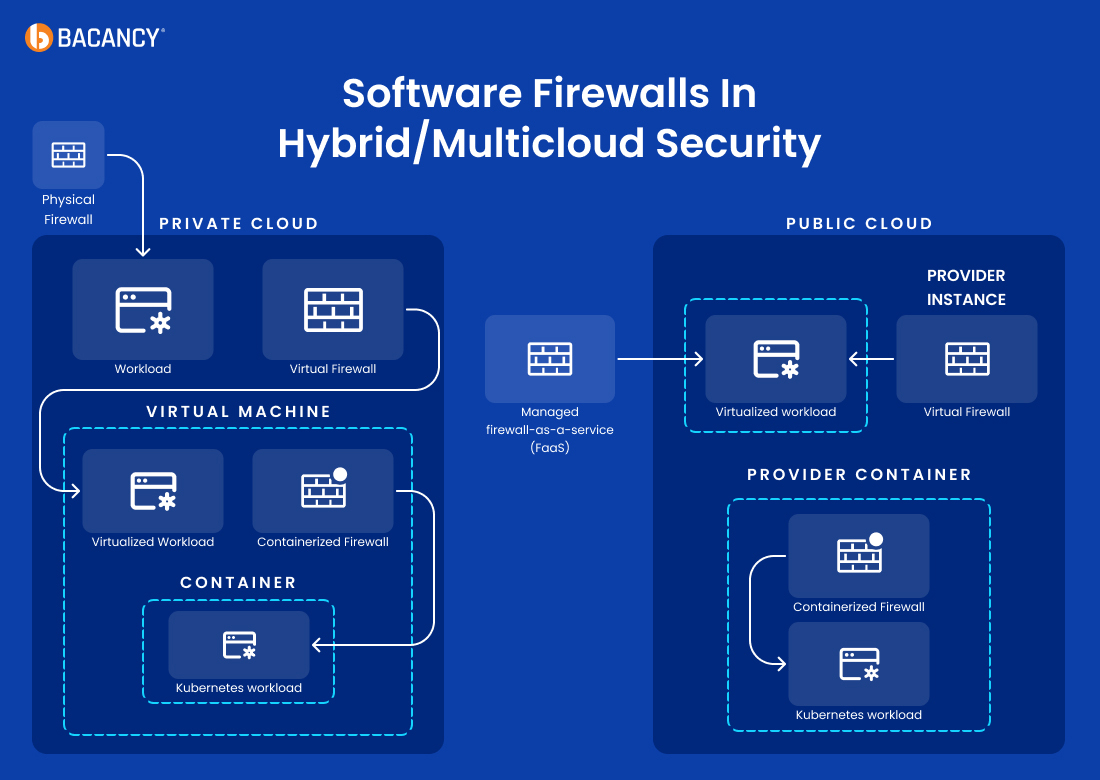
The organization has complete control over the infrastructure in a private cloud setup. Security here is typically layered as follows:
This layered approach ensures comprehensive protection from the network layer all the way to the application level within private environments.
In public cloud environments like AWS, Azure, or Google Cloud, security is often shared between the provider and the customer. Here’s how firewall protection works:
These firewalls apply fine-grained control at the container level in multi-tenant environments.
This setup ensures policies are enforced at multiple layers and adapts to the dynamic nature of public cloud infrastructure.
To build a resilient and secure hybrid cloud environment, organizations should implement three core types of controls: physical, technical, and administrative. These components work together to create a layered defense that protects infrastructure, data, applications, and users.
These secure the actual physical infrastructure supporting the hybrid cloud.
These are IT-based measures to protect systems, data, and applications in the hybrid environment.
These are human- and policy-based practices to guide secure behavior and planning.
Read more about cloud security threats and risks
Securing cloud environments is increasingly challenging as businesses scale across hybrid and multi-cloud setups. From misconfigurations to compliance gaps, here are 15 common cloud security challenges and how to mitigate them effectively.

Network-transmitted data is vulnerable to eavesdropping and man-in-the-middle attacks. Attackers can intercept or imitate trusted endpoints to gain access to sensitive information. Enterprise mobility managers must prioritize encryption to prevent such breaches.
Possible solutions:
Network administrators often need help identifying and preventing attacks due to a lack of comprehensive risk profiling of IT systems. This jeopardizes the security of hybrid clouds and makes it difficult to detect and stop breaches.
Possible solutions:
Ensuring compliance in a hybrid setup is complex, especially as data flows between public and private clouds. Misalignment with regulatory frameworks can lead to legal and operational issues.
Possible Solutions:
Many companies need help with security for hybrid cloud due to a lack of proper identity management and authentication across private and public clouds.
Possible Solutions:
A lack of redundancy in hybrid cloud environments can expose a company to risks, especially if data needs to be properly distributed across multiple data centers. This increases vulnerability to disruptions.
Possible solutions:

In hybrid cloud environments, managing user identities and access becomes complex due to different platforms using varied authentication methods. Unauthorized users may access sensitive data without proper verification, leading to breaches or compliance issues. This makes shared responsibility between the organization and cloud provider essential for secure access control.
Possible solutions:
Unprotected API endpoints can expose sensitive data to attacks where malicious actors manipulate authentication tokens to access personal information. This issue is especially concerning in enterprise mobility and Bring Your Own Device (BYOD) setups over insecure connections.
Possible solutions:
A Denial of Service (DoS) attack targets cloud or mobile services by flooding shared resources, such as CPU, memory, or network bandwidth, causing them to become overloaded. Poor resource management worsens the impact, leading to service disruptions and downtime.
Possible solutions:
While flow analytics can help manage traffic volume, its delayed response time often limits its effectiveness against fast-moving DoS and Distributed Denial of Service (DDoS) attacks.
Intellectual property (IP) requires enhanced protection through strong encryption and authentication protocols. To safeguard IP, it must be identified, classified, and assessed for vulnerabilities.
Possible solutions:
Ensure cloud vendors meet security standards when working with them. Businesses lose some control over their data once it’s deployed to the cloud, so understanding the vendor’s protection measures is crucial.
Possible solutions:

When organizations move their data to the cloud, they lose direct control and must rely on service providers to ensure proper protection, particularly in the public cloud. A lazily designed SLA might force you to face unwanted and unexpected challenges in managing hybrid cloud security.
Possible solutions:
Weak security protocols from cloud providers can lead to data being corrupted, deleted, or accessed without permission. The risk increases in BYOD setups, where employees use personal devices for work.
Possible solutions:
Effective hybrid cloud management requires a clear understanding of goals, defined roles, and strict policies. Without structured procedures, networks are vulnerable to attacks. A comprehensive approach is essential to managing hybrid infrastructure and overcoming hybrid cloud security vulnerabilities.
Possible solutions:
Managing activities across various domains in a hybrid cloud requires well-defined strategies and tools. Hybrid cloud security often considers limitations in cross-platform management, leading to inefficiencies. Companies must determine the right tools for seamless operations to avoid these pitfalls.
Possible solutions:
Insider threats are often overlooked but pose a serious risk to hybrid cloud security. Not all employees or insiders can be fully trusted; some may intentionally misuse access to sensitive data, leading to data breaches, service disruptions, or reputational damage.
Possible solutions:
Explore cloud managed services to streamline protection, ensure compliance, and secure every layer of your hybrid infrastructure.
With the hybrid cloud becoming a core part of modern infrastructure, securing it demands a proactive and unified approach. Implementing the proper security practices ensures data protection, compliance, and resilience across environments. Here are the top best practices to follow in 2025.
Define strict policies that only allow authorized, secure applications within your hybrid cloud environment. Block all unapproved or unknown apps to reduce risk exposure. Use network tools that classify traffic by application for complete visibility and control.
Move beyond IP-based security by integrating user and group identities into your access control policies. Ensure permissions are tied to the user, not just their device or location. This provides consistent, dynamic security as users move across environments.
Apply Zero-Trust principles by validating every user, device, and connection, no matter where they originate. Segment workloads and block known threats while inspecting unknown files. This approach limits lateral movement and reduces breach risk.
Select tools that can operate across virtualized, physical, and software-defined environments. They should scale with your infrastructure and evolve with your business needs. Flexibility ensures minimal disruption during growth or platform changes.
Enforce strong, consistent access policies for all users, including those on personal or remote devices. Protect both cloud and on-prem systems without compromising usability. This helps secure your hybrid environment in a distributed workforce.
Manage all firewall rules and security policies from a unified platform. Centralization ensures consistent enforcement across cloud and on-prem systems and allows for faster policy updates, especially during active threat scenarios.
Use security architectures built to protect both on-prem and cloud workloads. Extend legacy controls into the cloud and prevent lateral attacks between environments. Integration with cloud-native services boosts automation and efficiency.
Automate repetitive security tasks such as threat detection, access provisioning, and policy enforcement. This reduces human error and enhances response speed. It also frees up teams to focus on higher-value security strategies.
Hybrid cloud security is crucial for protecting your data, applications, and infrastructure across both private and public clouds. As more organizations choose hybrid cloud solutions to gain flexibility and cloud scalability, having strong security measures in place is vital to prevent risks and ensure smooth operations.
To achieve the best results, opt for cloud consulting services where experts can help you design and implement a robust hybrid cloud security strategy tailored to your business needs. This approach ensures reliable protection, compliance, and efficient management across your entire hybrid environment.
A hybrid cloud means using private and public clouds alongside traditional data centers. Since it involves data from multiple sources, this may increase challenges like security breaches, compliance failures, or vulnerabilities.
These issues are caused by data leakage, appropriate regulatory compliance, hiding complex security rules behind APIs, or even the lack of significant differences in the quality of security policies between on-premise and cloud-based systems.
Whether it is encrypting data in transit, implementing strong access controls, ensuring data sovereignty, regularly auditing security policies by businesses, or enforcing monitoring of logs.
The best practice involves enforcing security policies consistently, implementing multi-factor authentication, regularly monitoring cloud environments, integrating identity management systems, and maintaining consistent security across on-premise and cloud infrastructure.
Well, but it isn’t straightforward. Businesses need to ensure that no matter where it is, the cloud providers they work with provide solutions that comply with the specific industry regulations they adhere to — be that GDPR, HIPPA or PCI DSS- and have control over their critical data.
Your Success Is Guaranteed !
We accelerate the release of digital product and guaranteed their success
We Use Slack, Jira & GitHub for Accurate Deployment and Effective Communication.