Top 15 Ways AI in Cloud Security Can Help You Protect Cloud Workloads in 2026
Last Updated on February 6, 2026
Summary
AI is the future, but can it also secure your cloud workloads? In this blog, we highlight security challenges and the top 15 ways you can use AI in cloud security to seamlessly automate, protect, reduce manual effort, and keep your workflows stronger, safer, and more reliable.
Table of Contents
Ever wonder how one tiny slip can turn into a massive data disaster? Take February 2024, for example. Change Healthcare, part of UnitedHealth Group, got hit by the ALPHV/BlackCat ransomware gang. They walked away with personal and health info for over 190 million people, all because of stolen credentials and an outdated server. (Source: aha.org).
The attackers gained access using stolen credentials and an outdated Citrix server. Ransomware quickly spread across CVS Health, Walgreens, and BlueCross BlueShield of Montana. However, not all data was recovered after paying a 22-million-dollar ransom, showing that traditional security alone is no longer enough.
Crazy, right? One small mistake, and suddenly, your sensitive data is on the line. This is where AI comes in. In 2026, it helps companies stay ahead of threats by:
AI works quietly in the background, helping protect cloud workloads so your business can keep running without interruptions.
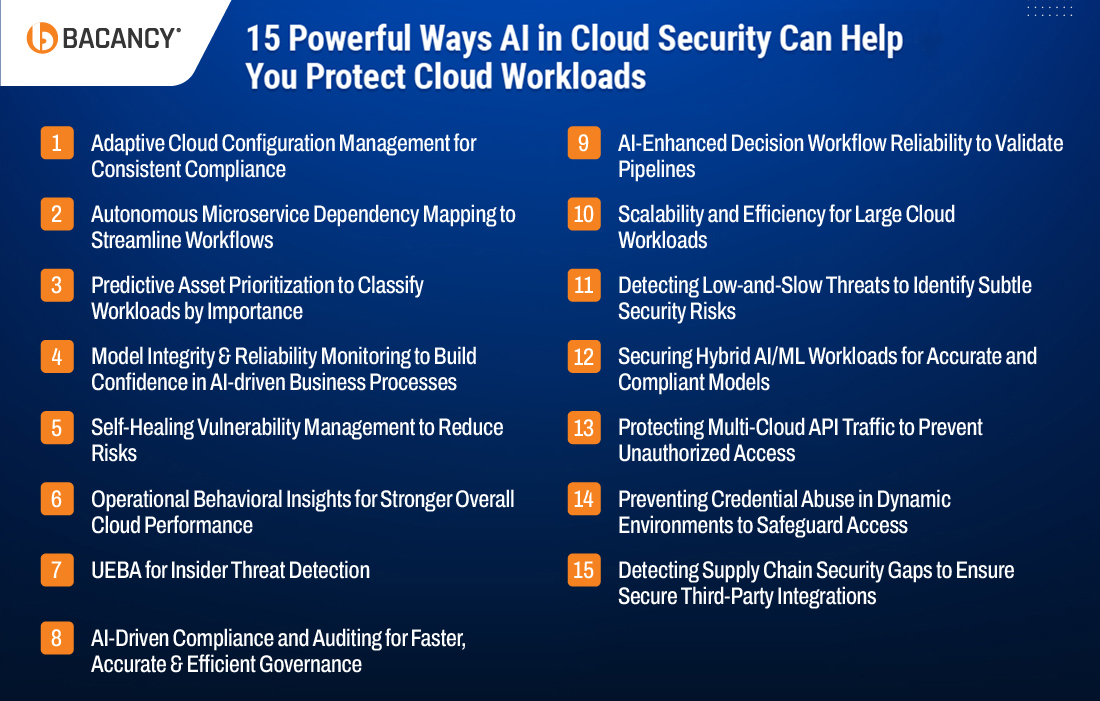
In this post, we’ll walk through 15 ways AI in cloud security is making systems smarter and more reliable in 2026, so you can keep your data safe and your operations running smoothly.
AI for cloud security is transforming how organizations protect their environments by enabling smarter, faster, and more precise defenses. These 15 cloud security use cases show how AI in cloud security can proactively safeguard workloads, reduce risk, and streamline security operations.
Managing cloud configurations requires proper alignment of IAM roles, network policies, storage permissions, and APIs across all cloud platforms.
Continuous review, policy simulation, and standards enforcement ensure optimized operations, strengthened security, and consistent compliance across the environment.
A global fintech company used an AI-based cloud security tool to monitor IAM roles and cloud storage permissions across AWS, Azure, and GCP. The tool detected a newly deployed Lambda function with excessive permissions, recommended stricter access, and simulated the change to ensure workflows continued safely.
Maintaining clear visibility of microservice interactions and serverless workflows is essential for optimizing operations, enabling seamless communication, and enhancing overall system performance.
Understanding these dependencies helps teams streamline workflows, reduce latency, and ensure smooth, efficient service delivery.
An e-commerce platform running Kubernetes, AWS Lambda, and Azure Functions, integrated Splunk AI and Dynatrace AI monitoring. The AI mapped service dependencies, detected unusual API calls from the payment service to a legacy inventory endpoint, and recommended throttling and updated access rules, preventing failed transactions and misconfigurations.
You need Predictive Asset Prioritization to classify workloads by importance, as it helps identify which assets are most critical, allocate monitoring and protection efficiently, and focus security efforts where they matter most.
By predicting asset risk and sensitivity, you can ensure high-value resources get continuous oversight, prevent potential threats from impacting key systems, and optimize resource use across your cloud environment.
A healthcare SaaS provider on AWS RDS, S3, and Azure SQL used Microsoft Sentinel AI analytics. The AI ranked assets by risk, highlighting the primary EHR database as most exposed due to cross-region replication. Security teams applied stricter encryption and tighter access policies, reducing potential HIPAA violations.
AI and ML models deliver their full potential when they operate with consistent inputs, validated pipelines, and reliable inference.
Maintaining ongoing monitoring and regular validation ensures accurate, trustworthy outputs, reduces errors in automated decisions, and builds confidence in AI-driven processes across your business.
A bank running fraud detection models on AWS SageMaker and Azure ML deployed AI-driven ML monitoring tools. The system checked incoming data and model outputs, detected anomalies from a new SageMaker model, quarantined the model, and triggered retraining workflows, preventing financial misclassifications.
Cloud workloads, including VMs, containers, serverless functions, and networks, need continuous monitoring for hidden or emerging vulnerabilities that could be exploited.
You need to monitor system configurations, patch levels, access controls, and network settings to reduce risk and maintain resilient workloads.
A SaaS provider with multi-region containers in EKS and AKS used AWS GuardDuty AI to scan for misconfigurations. When a container exposed sensitive ports publicly, AI applied correct network policies, patched vulnerabilities, and prevented potential attacks without human intervention.
Understanding normal activity patterns for users, services, and workloads helps identify anomalies and maintain smooth, efficient operations.
Leveraging this strategy provides continuous visibility, prevents disruptions, and enables teams to optimize workflows for stronger overall performance.
An online gaming platform on AWS and GCP used AI to analyze user and service activity. AI noticed unusual login spikes at 3 AM from a service account with excessive privileges and recommended access adjustments to keep operations smooth.
Monitoring privileged accounts, service accounts, and unusual access patterns through User and Entity Behavior Analytics (UEBA) helps identify early signs of insider threats and compromised credentials before they escalate.
Adopting this approach ensures enhanced visibility into user and entity behavior, strengthens oversight, and enables timely, targeted responses to high-risk activities that might otherwise go unnoticed.
A media company using Office 365, G Suite, and AWS IAM integrated UEBA AI tools like Exabeam AI and Splunk User Behavior Analytics. The AI monitored account activity, detected a marketing employee attempting to download large datasets outside working hours, temporarily blocked access, and alerted security teams before data leakage occurred.
Key areas like cloud configurations, user access controls, resource usage, encryption settings, and logging policies must be continuously monitored to ensure compliance with standards like CIS Benchmarks, SOC2, or ISO 27001.
Following these practices helps maintain alignment with industry frameworks, strengthens governance, and makes compliance management faster, more accurate, and more efficient.
A global manufacturing firm using Azure, AWS, and connected IoT devices deployed Microsoft Sentinel AI analytics. The AI scanned all cloud configurations in real time, comparing them against ISO 27001 and CIS Benchmarks. It detected unencrypted IoT data in an S3 bucket, applied the correct encryption automatically, and generated audit-ready reports, reducing manual effort and ensuring continuous compliance.
Partner with Bacancy’s cloud consulting services to secure workloads, simplify audits, and ensure business continuity.
AI/ML-driven workflows need to process data consistently and deliver accurate outputs to support dependable operations.
Using AI in cloud security to validate pipelines, monitor transformations, and secure each step ensures results remain trustworthy, protected, and free from errors.
A logistics company using Azure ML pipelines integrated AI-driven workflow monitoring tools. The AI monitored all pipeline stages and data transformations in real time, detected invalid routes caused by a corrupted CSV file, quarantined the affected pipeline, corrected the data automatically, and retrained the model, ensuring accurate route optimization decisions without manual intervention.
Securing large cloud environments means monitoring massive volumes of logs, events, and network flows across regions to maintain continuous visibility and control.
Understanding these patterns ensures faster detection of issues, smarter allocation of resources, and consistent protection at scale.
A multinational retailer using AWS CloudTrail, Azure Monitor, and GCP Stackdriver integrated AI-driven monitoring tools. These tools analyzed millions of daily events in real time, detected unusual spikes in checkout API requests across regions, prioritized incidents based on risk, and automatically triggered throttling to prevent system overload and potential fraud.
In cloud environments, it’s important to pay attention to subtle patterns that can indicate a potential breach. Accounts accessing unusual resources, irregular login times, and slow data transfers over weeks or months are signs that need careful monitoring.
Tracking these behaviors consistently and identifying anomalies early is essential to preventing small issues from turning into serious security incidents.
A healthcare provider’s AI security system flagged a developer account accessing patient records across multiple regions at unusual hours over several months. The investigation revealed a misconfigured backup process that exposed sensitive data. Early action prevented a HIPAA violation and costly breach.
AI and ML workloads often span cloud platforms such as AWS SageMaker, Azure ML, and on-prem environments. These distributed models rely on sensitive datasets and critical training pipelines, so unauthorized access, misconfigurations, or unexpected changes can affect predictions, compromise data integrity, and introduce compliance risks.
Closely tracking access and monitoring model operations is essential to ensure accuracy and security.
A financial services firm running fraud detection ML models used Azure Sentinel AI and UEBA tools to detect a researcher querying production models from an unregistered Azure VM. The system immediately blocked access, logged the incident, and sent detailed reports, protecting sensitive predictions and ensuring regulatory compliance.
APIs connecting AWS, Azure, and GCP handle large volumes of traffic and critical service integrations. Unusual request sequences, sudden usage spikes, or misconfigured integrations can introduce vulnerabilities, enabling attackers to steal data or escalate privileges. Monitoring API activity across multiple clouds is crucial to maintain security and operational continuity.
An e-commerce company integrating Shopify with AWS Lambda and Azure Logic Apps used AWS GuardDuty AI and Azure Sentinel AI to detect unusual bulk API requests. The system automatically blocked the requests and alerted the security team. Investigation revealed a compromised vendor integration, preventing large-scale data leakage.
Temporary cloud resources, ephemeral containers, and short-lived access keys (such as AWS IAM temporary credentials or Azure Managed Identities) can be misused for privilege escalation or unauthorized access. Monitoring these fast-changing credentials and identifying abnormal usage patterns is critical to maintaining secure cloud environments.
A SaaS platform managing ephemeral developer keys in Kubernetes used an AI-driven credential monitoring system to spot a key being accessed outside its assigned cluster and time window. The system automatically revoked the key, alerted administrators, and prevented unauthorized access to production databases.
Third-party services, vendor tools, and external integrations such as ERP systems, CRM plugins, and CI/CD pipelines can introduce hidden risks. Misconfigurations, insecure data flows, or non-compliant transfers may compromise sensitive information if not closely monitored.
Keeping track of these dependencies is essential to prevent potential security breaches.
A logistics company utilizing Salesforce, NetSuite, and a third-party shipment tracking SaaS had Azure AI Anomaly Detector identify a service transmitting shipment data over HTTP instead of HTTPS. The system isolated the service, alerted the security team, and recommended secure updates, preventing potential data exposure.
Here’s how you can implement AI and cloud security best practices to strengthen your environment and stay ahead of threats:

Continuously monitor who accesses cloud resources, how often, and for what purpose. With AI systems analyzing access logs and permissions, you can identify inactive accounts or users with excessive privileges and adjust access proactively.
Example: A financial services company used an AI system to scan AWS S3 access logs. It detected a developer account with full admin rights that hadn’t been used in months. The AI recommended revoking access, reducing the risk of misuse without affecting active workflows.
Combine AI with native security platforms like AWS GuardDuty, Azure Sentinel, or Google Security Command Center. Correlate events across tools to detect threats faster and uncover patterns that manual checks might miss.
Example: AI detected that a user had an unusual login in Azure AD while simultaneously attempting to access restricted S3 data in AWS. This correlated activity triggered an automated alert, preventing a potential cross-cloud breach.
Link AI to automation services such as AWS Systems Manager, Azure Logic Apps, or GCP Cloud Functions. This allows immediate actions against threats, reducing response times and human error.
Example: During a Kubernetes cluster breach, the AI system detected abnormal activity on one node, automatically isolated it, revoked suspicious IAM permissions, and alerted the security team, stopping lateral movement before sensitive data was compromised.
Monitor API usage in real time. AI can detect abnormal activity, flag misuse, and prevent unauthorized access to sensitive data.
Example: A SaaS company noticed unusual API calls that attempted to extract customer data. AI flagged these calls as anomalous, allowing the security team to block them before any data was exposed.
Not all resources are equally critical. Use AI to rank workloads by risk and apply stricter controls to high-value assets. Continuous monitoring ensures sensitive resources stay protected.
Example: An e-commerce platform used AI to identify the payment processing services that were most at risk. The platform then applied stricter access controls and continuous monitoring specifically for those services, reducing potential financial loss.
Cloud configurations change constantly, which can introduce vulnerabilities. Use AI to detect deviations from approved baselines and recommend corrective actions.
Example: An AI-integrated system noticed that a previously secure database had its encryption settings altered during an update. It automatically suggested reverting to the approved baseline, maintaining compliance and preventing exposure of sensitive data.
Use AI to analyze traffic and system behavior, predicting potential threats before they happen. Early detection helps prevent attacks like DDoS or lateral movement.
Example: A media company’s AI system detected unusual traffic spikes from an external IP, predicting a possible DDoS attack. Automated throttling and alerts allowed the IT team to mitigate the attack without downtime.
Bacancy provides advanced cloud security services using AI in cloud security to protect and automate your cloud workloads. Our solutions address cloud security threats and risks, ensure compliance, enable multi-cloud monitoring, and secure AI models to keep your environment safe and efficient. Here’s how we help:
With these AI-powered practices in place, our team ensures that your cloud environment stays protected, resilient, and optimized for safety.
AI in cloud security uses machine learning and artificial intelligence tools to monitor cloud environments, detect anomalies, automate threat responses, and enhance compliance. It helps organizations proactively secure workloads across AWS, Azure, GCP, and hybrid setups.
AI analyzes logs, user behavior, network traffic, and API calls in real time. It identifies unusual patterns, such as abnormal login attempts, sudden spikes in API requests, or misconfigurations, and prioritizes incidents based on risk.
Yes. Using User and Entity Behavior Analytics (UEBA), AI monitors account activity, detects unusual actions, and alerts security teams. It can even automatically isolate high-risk accounts to prevent potential data breaches.
AI continuously monitors configurations, access controls, encryption settings, and logging policies. It generates real-time dashboards, suggests remediation, enforces standards like CIS, SOC2, and ISO 27001, and automates audit reporting.
AI is especially effective for large-scale, multi-cloud workloads, including hybrid AI/ML pipelines, serverless functions, containers, databases, and APIs, where manual monitoring is challenging and risk exposure is high.
Yes. Advanced AI tools can detect vulnerabilities, recommend or apply corrections, enforce network policies, and patch systems without human intervention, reducing risk and operational overhead.
AI correlates events across AWS, Azure, GCP, and on-prem systems. It provides unified visibility, detects cross-cloud risks, harmonizes policies, and enables consistent protection across distributed workloads.
Absolutely. AI-driven monitoring tools can process millions of logs and events in real time, detect anomalies at scale, prioritize critical incidents, and optimize resource allocation, ensuring continuous cloud protection.
Your Success Is Guaranteed !
We accelerate the release of digital product and guaranteed their success
We Use Slack, Jira & GitHub for Accurate Deployment and Effective Communication.