Quick Summary
In this article, we examined cloud misconfigurations, their underlying causes, and the risks they introduce. By understanding these issues and following consistent best practices, organizations can maintain a secure, reliable, and efficient cloud environment while minimizing errors and operational disruptions.
Table of Contents
Introduction
Every week, organizations move more workloads to the cloud, chasing speed, scalability, and innovation. Yet, with every new deployment, we see the same critical mistake repeated, cloud misconfigurations left unnoticed. These mistakes may look small, but they create wide gaps for attackers, expose organizations to compliance breaches, and drive unnecessary costs.
The toughest part is handling cloud systems that never stand still, always adapting and expanding. Preventing those mistakes calls for consistent best practices, well-structured checklists, and ongoing oversight. In the sections ahead, we’ll cover the misconfigurations most likely to occur, the causes behind them, and practical steps to help you avoid them.
What are Cloud Misconfigurations?
Cloud misconfiguration is the incorrect setup of cloud resources, services, or security settings that results in unintended behavior within an environment. In simple terms, it represents the difference between how a cloud resource should be configured and how it is actually configured.
Since these mistakes are preventable, identifying and understanding misconfigurations is the first step toward creating a reliable and well-protected cloud environment.
Common Cloud Misconfigurations
Examine the mistakes that frequently occur in cloud setups and the risks they create if left unaddressed.
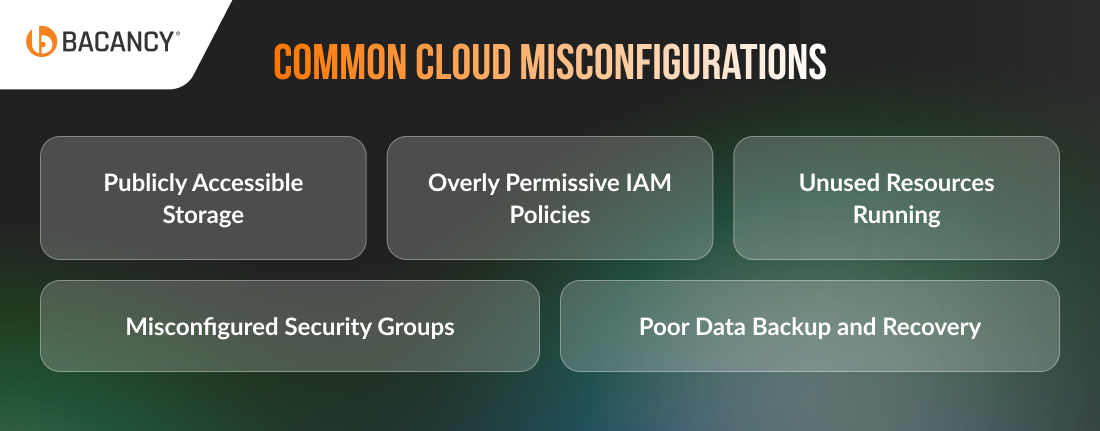
1. Publicly Accessible Storage
Storage buckets or databases left open to the public are often one of the biggest security blind spots in the cloud. Teams leave them public, sometimes due to default settings, sometimes due to skipped permissions. Once exposed, they act like open doors, making sensitive data an easy target and often leading to massive breaches.
2. Overly Permissive IAM Policies
To save time, users are often given broad “admin-like” permissions instead of fine-grained roles. This shortcut creates a massive risk. This creates unnecessary entry points, where a single compromised account could expose the entire environment.
3. Unused Resources Running
Many organizations spin up virtual machines, containers, or services for short-term needs but forget to shut them down. These idle resources silently add up on the monthly bill, consuming budgets without delivering value. Leveraging Cloud FinOps services can help track and optimize these resources effectively to save billions over time.
4. Misconfigured Security Groups
Security groups are supposed to restrict traffic, but they often get left wide open. A single “allow all” rule makes systems visible to the internet, inviting constant scans and intrusion attempts.
5. Poor Data Backup and Recovery
To be on the safe side, companies back up their data. The major safety step they avoid is testing recovery. The real problem appears during a system failure, when backups don’t work as expected and downtime drags on.
Top 4 Causes of Cloud Misconfigurations
Understand the underlying factors that lead to misconfiguration in cloud computing:

1. Rushed Deployments
After months of development, the deployment stage feels like the finish line. To speed things up, teams skip security reviews or postpone them. These “temporary” skips often stay unnoticed until an incident exposes the oversight.
2. Lack of Expertise
Cloud requires deep expertise to configure securely. Without the right knowledge and experience, teams often struggle with setting up permissions, networks, and storage the right way. If in-house expertise is missing, working with experienced cloud consultants from top companies can help avoid costly mistakes and strengthen overall security.
3. Poor Visibility and Monitoring
Cloud misconfiguration often slips through because teams don’t keep a close eye on their cloud resources. Without continuous logging, alerts, or regular reviews, exposed databases or public storage can remain vulnerable for weeks or even months before anyone notices.
4. Poor Governance and Policy Management
When governance is weak, policies are either too relaxed or inconsistently enforced. Teams may bypass rules to save time, and over months, these small exceptions pile up. This “policy drift” eventually leads to critical gaps.
Best Practices to Prevent Cloud Misconfigurations
Learn practical steps and proven strategies to secure your cloud environment, maintain proper configurations, and minimize risks through continuous monitoring and disciplined management.
1. Conduct Regular Security Audits
Make it a habit to audit your cloud environment regularly. Check permissions, storage, network settings, and other critical configurations. Regular security audits help you catch mistakes early, correct them before they escalate, and maintain a secure, well-organized cloud environment.
2. Apply the Principle of Least Privilege
Always give users only the access they truly need, no more, no less. Review permissions often and remove anything unnecessary. This prevents accidental changes, misuse and ensures that your cloud environment stays under control.
3. Keep Your Cloud Under Constant Watch
Always know what’s happening in your cloud. Set up alerts, track activity, and watch for anything unusual. When you spot problems early, you can fix them immediately and prevent small issues from turning into major disruptions.
4. Automate Cloud Configuration Management
Let automation handle routine checks for you. Cloud automation tools can scan your setup, flag any cloud security misconfiguration, and ensure everything follows best practices. This keeps your environment consistent, reduces human error, and saves your team valuable time.
5. Standardize Your Deployment Process
Make it a rule to use the same templates, workflows, and checklists every time you deploy resources. Standardizing your deployments ensures nothing important gets skipped, everything is configured properly, and your cloud remains predictable and reliable, even when deadlines are tight.
6. Train Your Teams Continuously
Keep your teams up to date with regular training. Teach them the latest cloud practices, new features, and common mistakes to avoid. When your staff are well-informed, they are confident, make fewer errors, and manage your cloud environment much more efficiently.
Conclusion
We’ve explored the most common cloud misconfigurations, why they occur, and practical steps to prevent them. From mismanaged permissions to unmonitored storage, these mistakes may seem small but can create serious security gaps, increase costs, and disrupt operations.
Even with regular audits, least-privilege access, continuous monitoring, and team training, managing a dynamic cloud environment can still be complex. This is where cloud security services provide a real advantage. With the right guidance, your cloud becomes not just functional but a strong foundation for growth and business success.